Stuxnet Computer Worm Targets Iranian Nuclear Plant

The security research world is oohing and ahhing lately at what may turn out to be the most sophisticated malware attack ever: Stuxnet.
Stuxnet appears to be more than just another malware attack, and more than just another targeted attack. Many believe that it is a government-sponsored attack against Iran’s nuclear facilities.
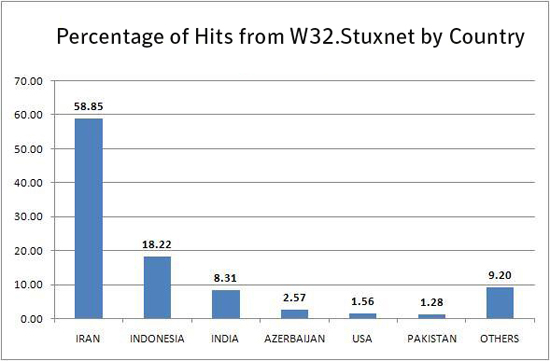
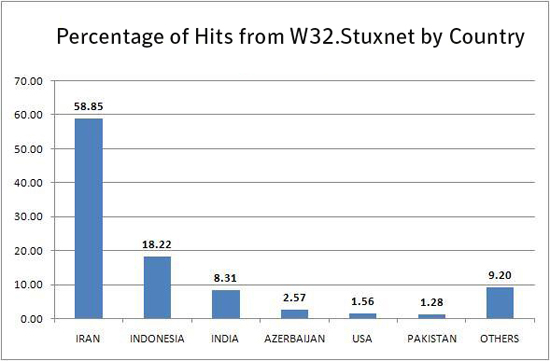
Top cybersecurity experts are warning that the Stuxnet worm represents a new type of cyberthreat — a cyberweapon created to cross into the physical world from the digital world to destroy something. Iran’s Bushehr nuclear power plant may be a target. Stuxnet so far has infected at least 45,000 industrial control systems around the world.
The Stuxnet computer worm spreads through previously unknown holes in Microsoft’s Windows operating system and then looks for a type of software made by Siemens and used to control industrial components, including valves and brakes.
<!–more–>
Stuxnet can hide itself, wait for certain conditions and give new orders to the components that reverse what they would normally do, the experts said. The commands are so specific that they appear aimed at an industrial sector, but officials do not know which one or what the affected equipment would do.
While cyber attacks on computer networks have slowed or stopped communication in countries such as Estonia and Georgia, Stuxnet is the first aimed at physical destruction and it heralds a new era in cyberwar.
At a closed-door conference this week in Maryland, Ralph Langner, a German industrial controls safety expert, said Stuxnet might be targeting not a sector but perhaps only one plant, and he speculated that it could be a controversial nuclear facility in Iran.
“What (the cyber worm) Stuxnet represents is a future in which people with the funds will be able to buy an attack like this on the black market. This is now a valid concern.”
The report said the encrypted, complex worm has not been immediately understood, and it employs new maneuvers, such as taking control of a computer system without the user taking any action or clicking any link, just inserting an infected memory stick.
The United States and Israel are two countries that could engineer such a threat, the report said.