Hackers Roll Call

The following list of Security Researchers are “White Hat” ethical hackers whose discoveries and inventions shake things up as they try to stay one step ahead of their underground “Black Hat” brothers…
It’s not unusual to hear someone say “Rsnake found out…” and Hansen’s manic inventiveness includes the “Slowloris” low-bandwidth denial-of-service tool, which ended up being used by anti-Iranian protesters to attack the Iranian leadership Web sites; another called “Fierce” does DNS enumeration to find non-contiguous IP space to make attacking targets easier.
Since 1998 has been investigating rootkits and buffer overflows, founded the Rootkit Web site and also co-authored the books “Rootkits, Subverting the Windows Kernel” and “Exploiting Software.” One of his most memorable feats was exposing vulnerabilities associated with the online game World of Warcraft, detailed in a book he co-authored with security expert Gary McGraw, “Exploiting Online Games.”

History may remember Kaminsky as the diplomat and statesman in the “White Hat” because of his work behind the scenes with software and service providers to patch a flaw he discovered in 2008 in the DNS protocol, which if exploited, would have led to mass disruption of the Internet. Though some argued he should have immediately disclosed the flaw, others praised his discretion in quietly working to fix the problem before it was widely publicized.
This co-author of “Hacking Exposed: Web 2.0″ and contributing editor to “Hacking VoIP” and “Mobile Application Security” digs into flaws in mobile and VoIP systems. In the past, some of his public talks and demos about compromising VoIP systems have been so detailed that chief information security officers at major corporations said they couldn’t advocate investing in VoIP until the issues raised were addressed by vendors.

Once the bad boy ‘Chameleon’ in hacking group ‘Rhino9,’ Maiffret luckily realized his hacking skills could be put to use in protecting Windows-based computers when, at age 17, he turned over a new leaf to co-found eEye Digital Security in 1997, working with security researchers Derek Soeder and Barnaby Jack. A demon at discovering Windows-based vulnerabilities, Maiffret also played a role in zeroing in on the infamous “Code Red” worm in 2001, which exploded across the Internet ravaging Microsoft-based computers.
Co-author of the “Mac hacker’s handbook,” Miller has hacked Safari for the last three years at the Pwn2Own contest, found an iPhone exploit that consisted entirely of SMS text messages, and was the first to hack Apple’s iPhone in 2007 and the Android phone in 2008. He also is credited with writing the first “virtual world” exploit for Second Life.
The open-source penetration testing platform, the Metasploit Project, founded in 2003 by Moore as chief architect, has become one of the most influential security inventions of the era with its penetration-testing and exploits used to uncover network weaknesses…by the good, the bad and the ugly.

This brainy Polish researcher has made it an obsession to figure out how stealth malware, such as rootkits, can be so well hidden in software and hardware that few are ever likely to find it. Her “Blue Pill” attack against Microsoft’s Vista kernel protection mechanism, which brought a crowded room of security geeks at Black Hat to a standing ovation in 2006, was just her first revelation publicly to show how easy it is for dangerous code to hide in plain sight.

Like Rutkowska, researcher Sparks has made rootkits and stealth malware her pursuit, and at one Black Hat Conference showed how operating system-independent rootkits, such as the proof-of-concept System Management Mode-based rootkit she built with colleague and co-founder Shawn Embleton, could be used to subvert and compromise computer networks.
With expertise in tracking malware and botnets used by cyber-criminals for financial gain, Stewart is often the first to identify dangerous new code specimens and how they work, such as the elusive Clampi Trojan and how the SoBig worm was sending spam. It all gives him an unpleasantly close look at East European and Chinese cyber-gang activity.
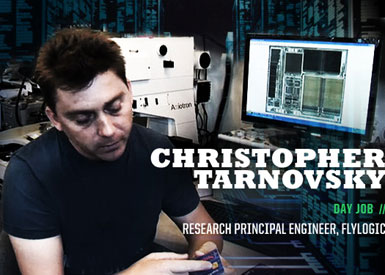
Like a surgeon re-tooling a pulsing heart, Tarnovsky makes use of specialized tools in his lab to bypass supposedly tamper-resistant hardware circuitry in semiconductors to gain root control to tap into data. As described in a Black Hat session, he did this recently with the Infineon processor with the Trusted Platform Module used in PCs, smart cards and even Microsoft’s Xbox. Others aren’t likely to duplicate his feats. Or are they?

Co-author of the “Mac Hacker’s Handbook” and “The Art of Software Security Testing,” Dai Zovi discovered and exploited a multi-platform security vulnerability in Apple’s QuickTime for Java in one night in order to hack a fully patched MacBook Pro to win the first Pwn2Own competition. He also was the first to publicly demonstrate VM hyperjacking using Intel VT-x in a live demo at Black Hat 2006. He says he can’t discuss “the hardest things” he ever hacked since that gets into non-disclosure agreement territory.


